QUESTION 111
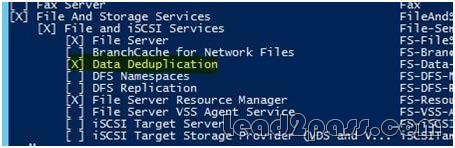
You manage an environment that has many servers. The servers run Windows Server 2012 R2 and use iSCSI storage. Administrators report that it is difficult to locate available iSCSI resources on the network. You need to ensure that the administrators can locate iSCSI resources on the network by using a central repository. Which feature should you deploy?
A. The iSCSI Target Server role service
B. The iSNS Server service feature
C. The Windows Standards-Based Storage Management feature
D. The iSCSI Target Storage Provider feature
Answer: B
Explanation:
A. iSNS facilitates automated discovery, management, and configuration of iSCSI and Fibre Channel devices (using iFCP gateways) on a TCP/IP network.
C. Windows Server 2012 R2 enables storage management that is comprehensive and fully scriptable, and administrators can manage it remotely
D. iSCSI Target Server enables you to network boot multiple computers from a single operating system image that is stored in a centralized location
http://technet.microsoft.com/en-us/library/cc772568.aspx
http://technet.microsoft.com/en-us/library/hh831751.aspx
http://technet.microsoft.com/en-us/library/dn305893.aspx
QUESTION 112
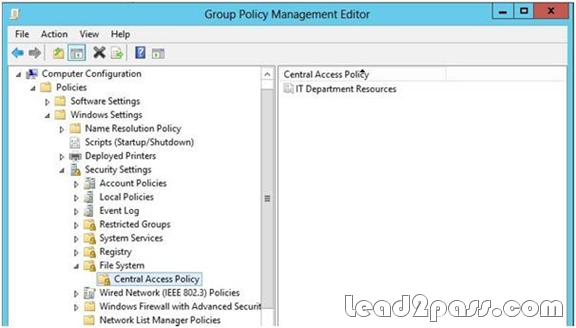
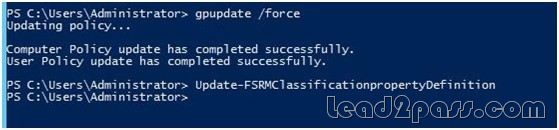
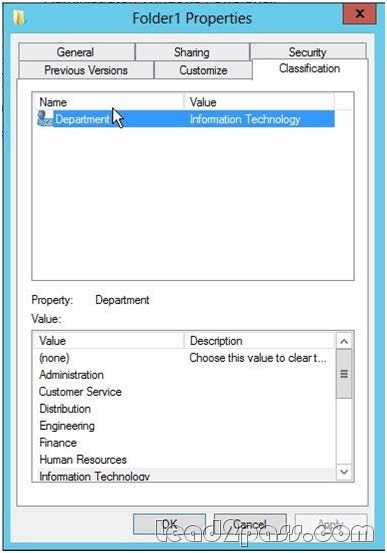
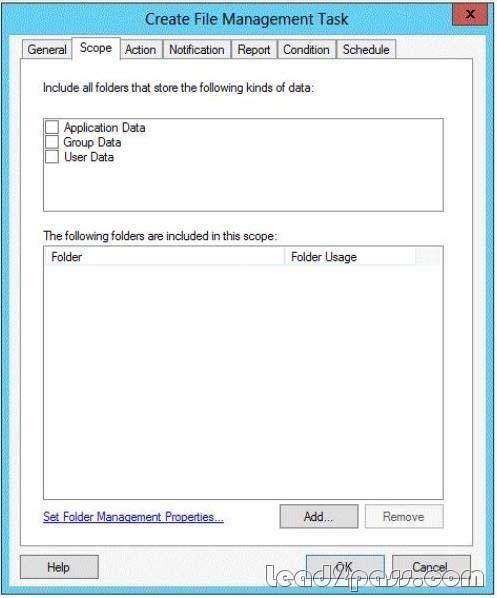
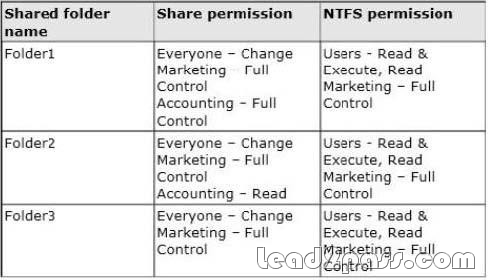
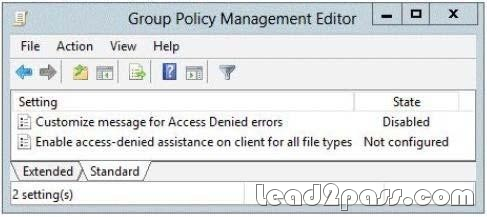
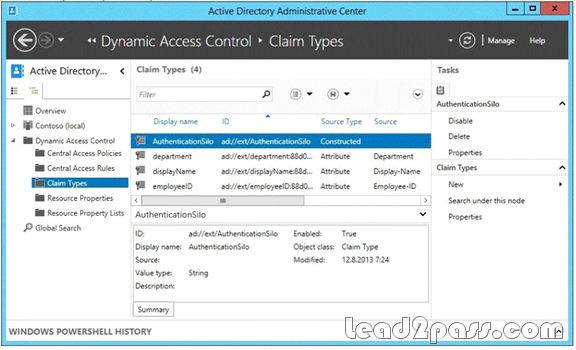
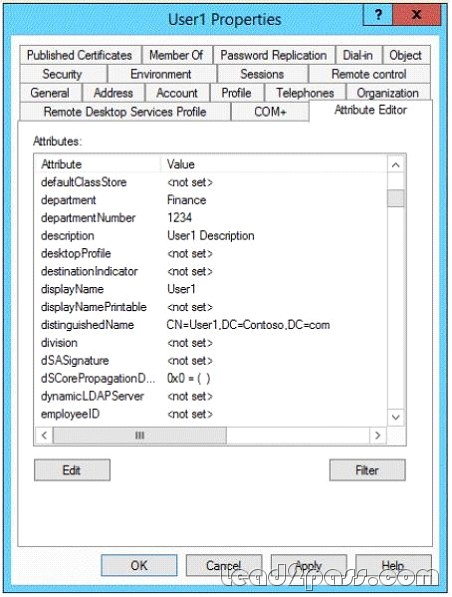
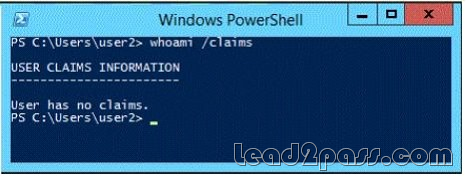
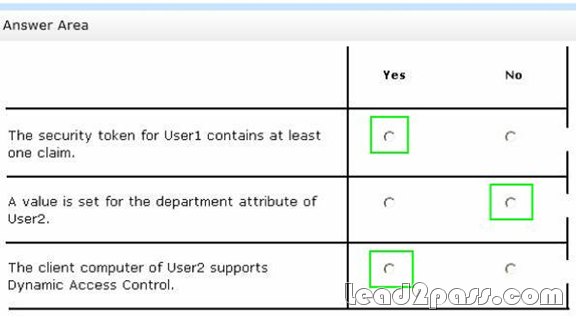
Your network contains an Active Directory domain named contoso.com. The network contains a file server named Server1 that runs Windows Server 2012 R2. You create a folder named Folder1. You share Folder1 as Share1. The NTFS permissions on Folder1 are shown in the Folder1 exhibit. (Click the Exhibit button.)
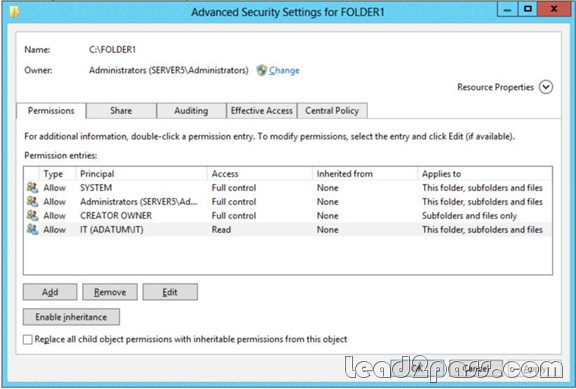
The Everyone group has the Full control Share permission to Folder1. You configure a central access policy as shown in the Central Access Policy exhibit. (Click the Exhibit button.)
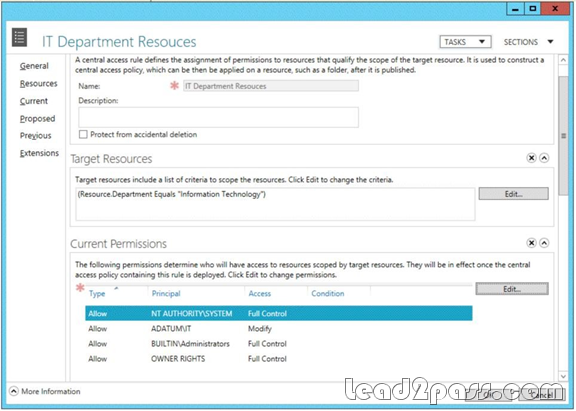
Members of the IT group report that they cannot modify the files in Folder1. You need to ensure that the IT group members can modify the files in Folder1. The solution must use central access policies to control the permissions. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. On the Classification tab of Folder1, set the classification to Information Technology.
B. On the Security tab of Folder1, add a conditional expression to the existing permission entry for
the IT group.
C. On Share1, assign the Change Share permission to the IT group.
D. On the Security tab of Folder1, remove the permission entry for the IT group.
E. On the Security tab of Folder1, assign the Modify permission to the Authenticated Users group.
Answer: AE
Explanation:
Central access policies for files enable organizations to centrally deploy and manage authorization policies that include conditional expressions that use user groups, user claims, device claims, and resource properties. (Claims are assertions about the attributes of the object with which they are associated). For example, to access high-business-impact (HBI) data, a user must be a full-time employee, obtain access from a managed device, and log on with a smart card. These policies are defined and hosted in Active Directory Domain Services (AD DS). http://technet.microsoft.com/en-us/library/hh846167.aspx
QUESTION 113
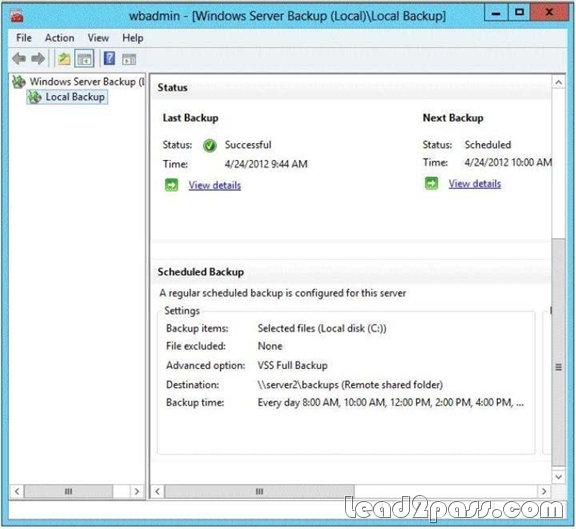
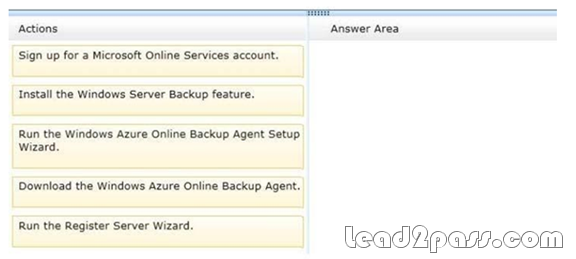
You have a server named File1 that runs Windows Server 2012 R2. Fuel has the File Server role service installed. You plan to back up all shared folders by using Microsoft Online Backup. You download and install the Microsoft Online Backup Service Agent on File1. You need to ensure that you use Windows Server Backup to back up data to Microsoft Online Backup. What should you do?
A. From Computer Management, add the File1 computer account to the Backup Operators group.
B. From Windows Server Backup, run the Register Server Wizard.
C. From a command prompt, run wbadmin.exe enable backup.
D. From the Services console, modify the Log On settings of the Microsoft Online Backup Service Agent.
Answer: B
Explanation:
A. Enables you to back up and restore your operating system, volumes, files, folders, and applications from a command prompt.
B. To register a server for use with Windows Azure Backup you must run the register server wizard
http://technet.microsoft.com/en-us/library/hh831677.aspx
QUESTION 114
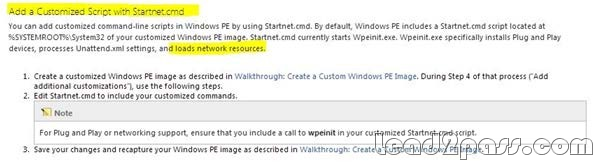
Your network contains an Active Directory domain named contoso.com. You are creating a custom Windows Recovery Environment (Windows RE) image. You need to ensure that when a server starts from the custom Windows RE image, a drive is mapped automatically to a network share. What should you modify in the image?
A. startnet.cmd
B. Xsl-mApp1ngs.xml
C. Win.ini
D. smb.types.ps1xml
Answer: A
Explanation:
The best way to define what to start is using starnet.cmd
http://technet.microsoft.com/en-us/library/cc766521(v=ws.10).aspx
QUESTION 115
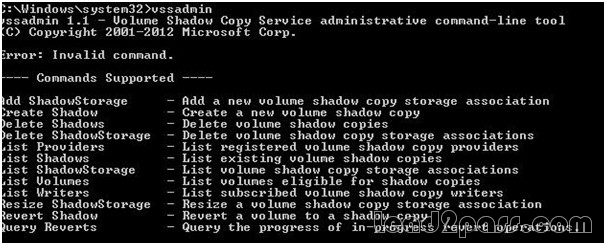
You have a file server named Server1 that runs a Server Core Installation of Windows Server 2012 R2. You need to ensure that users can access previous versions of files that are shared on Server1 by using the Previous Versions tab. Which tool should you use?
A. Diskpart
B. Wbadmin
C. Vssadmin
D. Storrept
Answer: C
Explanation:
A. Enables you to back up and restore your operating system, volumes, files, folders, and applications from a command prompt.
B. DiskPart is a text-mode command interpreter that enables you to manage objects (disks, partitions, volumes, or virtual hard disks) by using scripts or direct input from a command prompt. C. The storrept command is installed with File Server Resource Manager and includes
subcommands for creating and managing storage reports and storage report tasks, as well as for configuring general administrative options for File Server Resource Manager.
D. Displays current volume shadow copy backups and all installed shadow copy writers and providers. To view the command syntax for any of the commands in the following table, click the command name.
http://technet.microsoft.com/en-us/library/cc754015(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc770877(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc753567(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc754968.aspx
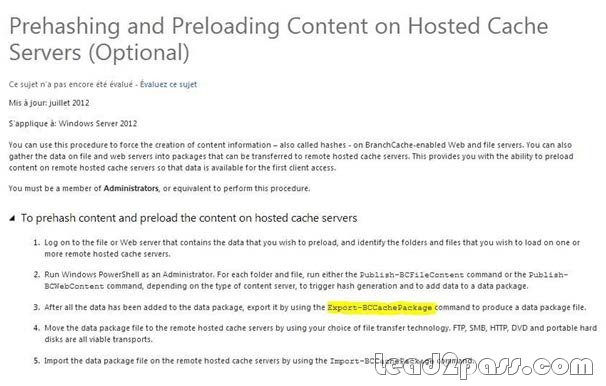
QUESTION 116
Your company has a main office and a branch office. The main office contains a file server named Server1. Server1 has the BranchCache for Network Files role service installed. The branch office contains a server named Server2. Server2 is configured as a BranchCache hosted cache server. You need to preload the data from the file shares on Server1 to the cache on Server2. You generate hashes for the file shares on Server1. Which cmdlet should you run next?
A. Add-BCDataCacheExtension
B. Set-BCCache
C. Publish-BCFileContent
D. Export-BCCachePackage
Answer: D
Explanation:
A. increases the amount of cache storage space that is available on a hosted cache server by adding a new cache file.
B. Modifies the cache file configuration.
C. Generates hashes, also called content information, for files in shared folders on a file server that have BranchCache enabled and the BranchCache for Network Files role service installed.
D. Exports a cache package
http://technet.microsoft.com/en-us/library/hh848405.aspx
http://technet.microsoft.com/en-us/library/hh848413.aspx
http://technet.microsoft.com/en-us/library/hh848412.aspx
http://technet.microsoft.com/en-us/library/hh848409.aspx
http://technet.microsoft.com/fr-fr/library/jj572970.aspx
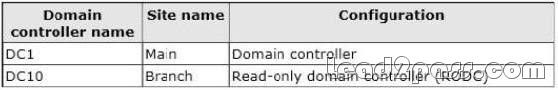
QUESTION 117
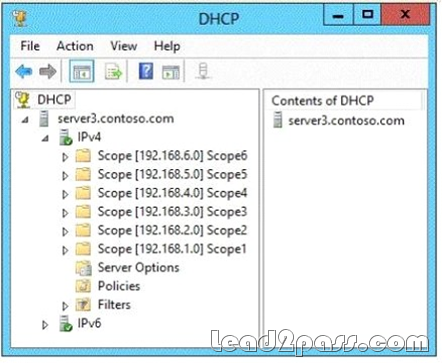
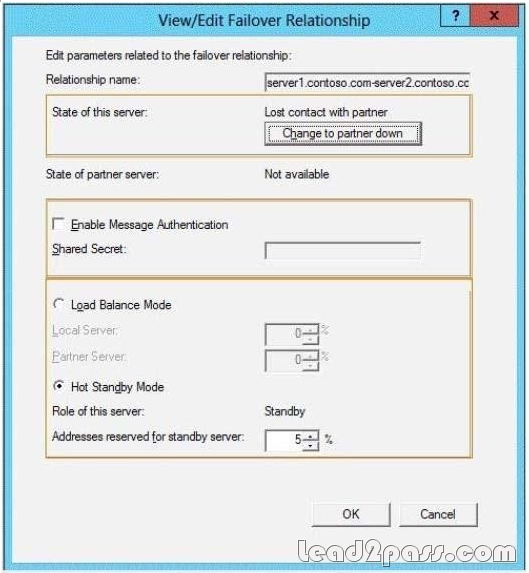
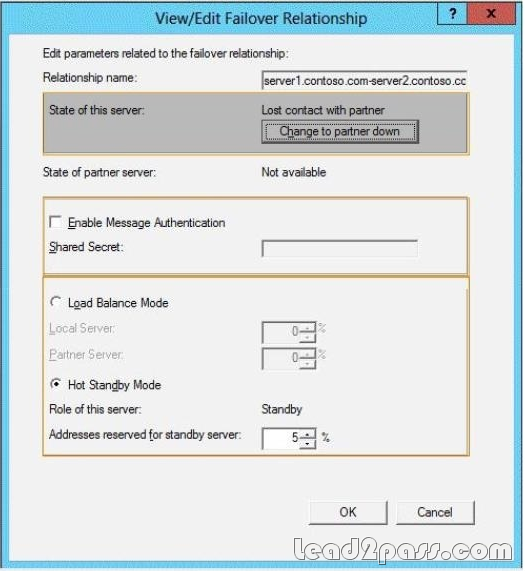
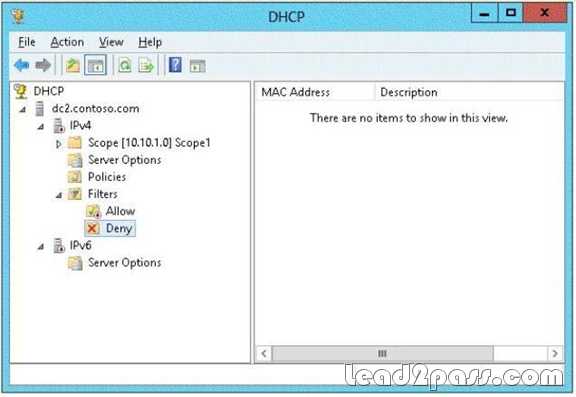
Your network contains an Active Directory domain named contoso.com. The domain contains a main office and a branch office. An Active Directory site exists for each office. The domain contains two servers named Server1 and Server2 that run Windows Server 2012 R2. Both servers have the DHCP Server server role installed. Server1 is located in the main office site. Server2 is located in the branch office site. Server1 provides IPv4 addresses to the client computers in the main office site. Server2 provides IPv4 addresses to the client computers in the branch office site. You need to ensure that if either Server1 or Server2 are offline, the client computers can still obtain IPv4 addresses.
The solution must meet the following requirements:
- The storage location of the DHCP databases must not be a single point of failure.
- Server1 must provide IPv4 addresses to the client computers in the branch office site only if Server2 is offline.
- Server2 must provide IPv4 addresses to the client computers in the main office site only if Server1 is offline.
Which configuration should you use?
A. load sharing mode failover partners
B. a failover cluster
C. hot standby mode failover partners
D. a Network Load Balancing (NLB) cluster
Answer: C
Explanation:
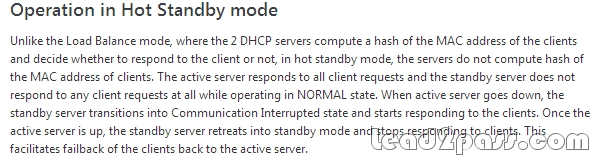
http://blogs.technet.com/b/teamdhcp/archive/2012/09/03/dhcp-failover-hot-standby-mode.aspx
http://blogs.technet.com/b/teamdhcp/archive/2012/09/03/dhcp-failover-hot-standby-mode.aspx
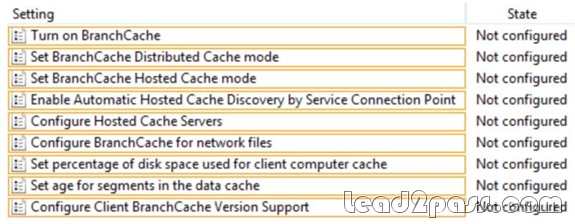
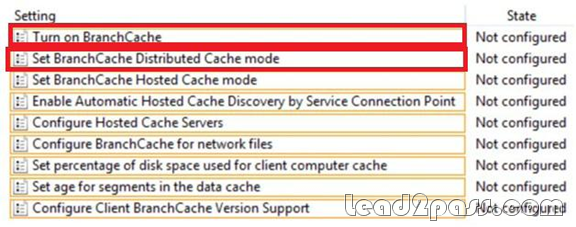
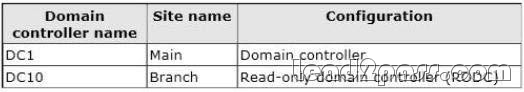
QUESTION 118
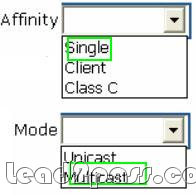
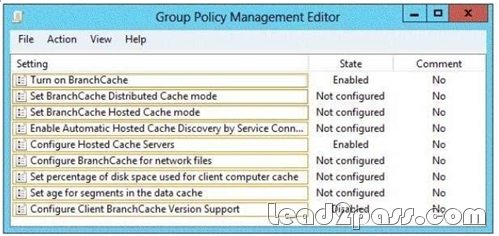
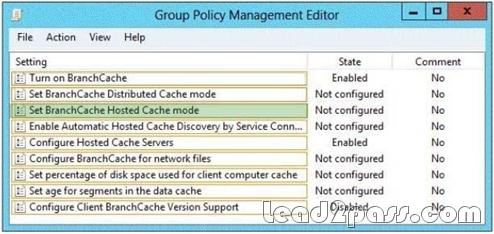
Your company has a main office and a branch office. The main office is located in Detroit. The branch office is located in Seattle. The network contains an Active Directory domain named adatum.com. Client computers run either Windows 7 Enterprise or Windows 8 Enterprise. The main office contains 1,000 client computers and 50 servers. The branch office contains 20 client computers. All computer accounts for the branch office are located in an organizational unit (OU) named SeattleComputers. A Group Policy object (GPO) named GPO1 is linked to the SeattleComputers OU. You need to configure BranchCache for the branch office.
QUESTION 119
You have a server named Server 1 that runs Windows Server 2012 R2. Server1 has five network adapters. Three of the network adapters are connected to a network named LAN1. The two other network adapters are connected to a network named LAN2. You create a network adapter team named Team1 from two of the adapters connected to LAN1. You create a network adapter team named Team2 from the two adapters connected to LAN2. A company policy states that all server IP addresses must be assigned by using a reserved address in DHCP. You need to identify how many DHCP reservations you must create for Server1. How many reservations should you identify?
A. 2
B. 3
C. 5
D. 7
Answer: B
Explanation:
3 adapter on LAN 1
2 adapters on LAN 2
2 adapters on LAN 1 used in a team, so that’s 3 – 2 leaving 1. 2 adapaters on LAN 2 used in a team, so that’s 2 – 2 leaving 0. 1 team on LAN 1 + 1 team on LAN 2 + remaining adapter on LAN 1 = 3.
QUESTION 120
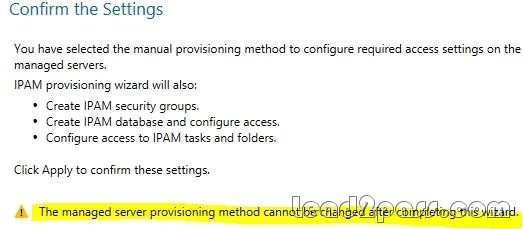
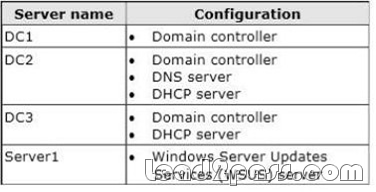
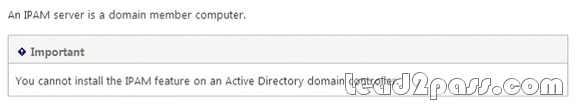
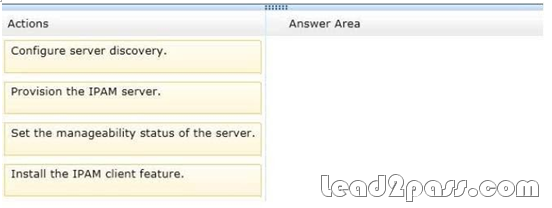
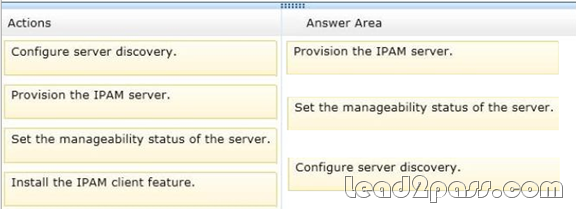
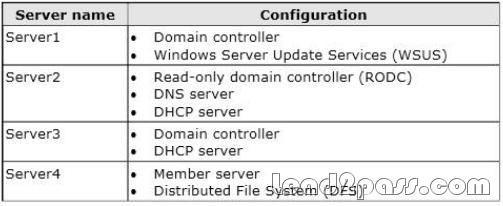
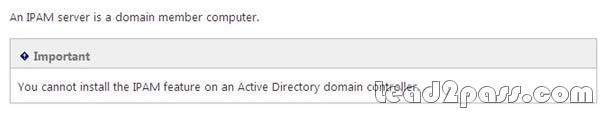
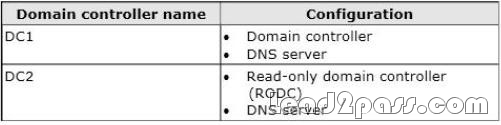
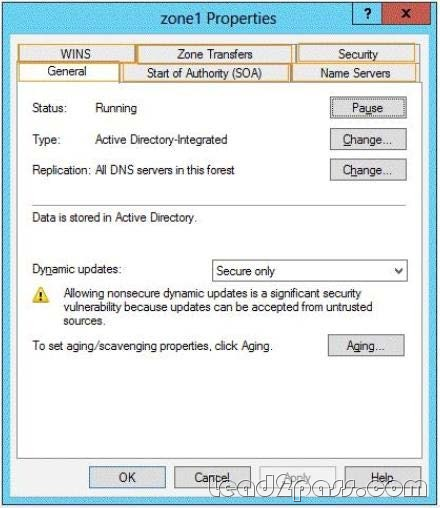
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the IP Address Management (IPAM) Server feature installed. IPAM is configured currently for Group Policy-based provisioning. You need to change the IPAM provisioning method on Server1. What should you do?
A. Run the ipamgc.exe command.
B. Run the Set-IPAMConfiguration cmdlet.
C. Reinstall the IP Address Management (IPAM) Server feature.
D. Delete IPAM Group Policy objects (GPOs) from the domain.
Answer: C
Explanation:
You cannot change the provisioning method after completing the initial setup.
If you want to pass Microsoft 70-412 successfully, donot missing to read latest lead2pass Microsoft 70-412 practice exams.
If you can master all lead2pass questions you will able to pass 100% guaranteed.